Centre for Geotechnical Science and Engineering
Rockfall Hazard Assessment
Rockfall research in Australia
Key Researchers: Anna Giacomini, Olivier Buzzi, Klaus Thoeni, Stephen Fityus
PROBLEM DESCRIPTION
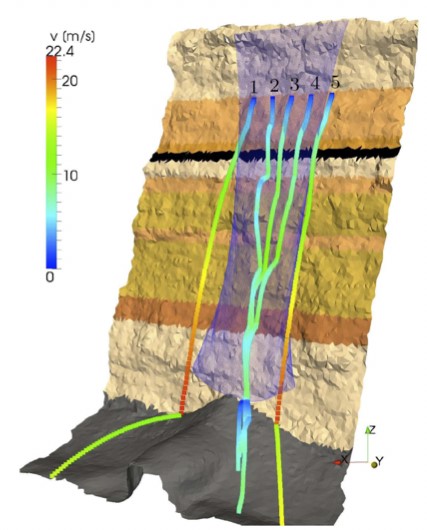
Rockfall presents a significant risk to users and infrastructure in coastal and mountainous areas, along transport corridors, and in most mining environments. Assessing the risk involves identifying and characterising the potentially unstable blocks, evaluating their trajectory and producing a risk zonation. Our research team developed a new rockfall hazard assessment methodology, named Evolving Rockfall Hazard Assessment (ERHA) for a quick identification of the most hazardous sections at the base of an extended rock face. The methodology can be also applied to civil environments. ERHA allows the quick identification of the sections with high hazard levels, where a strict quantitative hazard assessment is recommended. Besides the expected rockfall energy and rockfall activity, the methodology provides practitioners with key information regarding the standoff distance at the base of the rock faces and it represents a useful tool for providing greater confidence in locating personnel, machineries, and infrastructures at the toe of steep rock surfaces. The method is combined with advanced 3D modelling and last generation of surface monitoring to provide a rigorous quantitative assessment and design and location optimisation of mitigation measures.
SCIENTIFIC AND ENGINEERING APPROACHES
- Geostructural characterisation of rock faces using remote sensing and 3D reconstruction to characterise distribution, volume and location of potential unstable blocks.
- In situ tracking of block trajectory and computer modelling of trajectory using in-house code.
- Trajectory modelling using commercial and in-house DEM and FEM codes.
- Modelling of full protection structures (drapery systems, low energy barriers) including characterisation of effect of block size on the response of the system.
APPLICATIONS
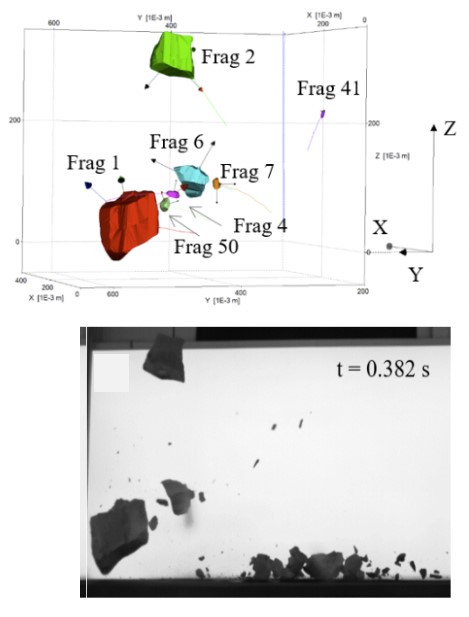
- Estimation of rockfall impact energy accounting for fragmentation.
- Design and optimisation of rockfall protection systems
- Qualitative and Quantitative rockfall risk assessment in mining and civil environments

The University of Newcastle acknowledges the traditional custodians of the lands within our footprint areas: Awabakal, Darkinjung, Biripai, Worimi, Wonnarua, and Eora Nations. We also pay respect to the wisdom of our Elders past and present.
